
As a cyber attack continues to cause severe disruption to global currency dealer Travelex, chief executives and CIOs in the finance industry face a stark question in 2020 – will we be next? In a special report, John Maslen talks to industry experts about what business leaders must do to prevent successful attacks.
“The first thing to learn from this is that all organisations are at risk because everyone has something of value to lose.”
Global currency dealer Travelex is entering its third week of disruption following a New Year’s Eve cyber attack that crippled key systems and led to it being taken offline.
On December 31, 2019, the company detected a software virus that had compromised some of its services; as a precautionary measure it immediately shut off internet access to prevent the spread of the virus further across the network.
The move affected 30 countries where it operates along with key customers who use its services including major banks.
The cause was the software virus Sodinokibi, also commonly referred to as REvil, which aims to encrypt a victim’s data and only provide an unlock code in return for a ransom.
According to the BBC, a cyber gang has claimed responsibility for the attack and demanded as much as $6m to prevent it releasing customer information.
McAfee, the cyber security company, has linked previous Sodinokibi attacks to Iran.
Tony D'Souza, chief executive of Travelex, said in a statement: “Our focus is on communicating directly with our partners and customers to protect them and their information from any further compromise. We are working tirelessly to bring our systems back online."
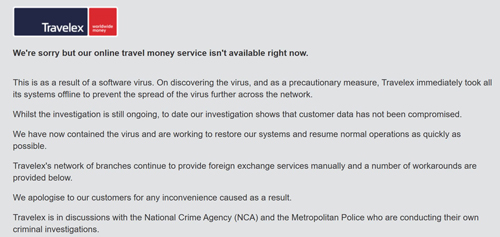
Travelex is in discussions with the National Crime Agency (NCA) and the Metropolitan Police and regulators worldwide on the issue.
Shares in Finablr, the London-listed parent company of Travelex, have plummeted since the announcement and the shockwaves from the attack have spread throughout the industry.
Call for action
In response, companies are being urged to consider their own processes for preventing cyber crime.
Will LaSala, senior director of global solutions at OneSpan, which has developed security and anti-fraud solutions for more than half of the world’s top 100 banks and thousands of other enterprises, including the US government, said: “Having proper processes and procedures in place will help organisations analyse what is happening and detect the necessary actions to stop bad actors in their tracks, before they can cause huge damage.
“But processes alone are sometimes not enough, and this is where technologies that automatically harden backend and client-side systems can help organisations face potential insider attacks head on.”
Mobile apps are seen as a weak point in company defences, he warned and added: “This incident should be a lesson to all finance companies that mobile app security, whether its developed in-house or outsourced, needs to consider the best security mechanisms to protect the app and the brand.”
Learning lessons from past incidents is critical and it can inform the development of measures designed to keep hackers at bay, said James Smith, principal security consultant and head of penetration testing at Bridewell Consulting.
Processes should include replicating data, off-site backups, network segregation, firmware updates and even routine simulations of attacks, along with response plans should an incident take place, so that the wider business is kept informed along with customers and the authorities.
He added: “The first thing to learn from this is that all organisations are at risk because everyone has something of value to lose. Whether that’s access to systems, intellectual property or customer data.
“The second thing to learn is that having a plan in place to mitigate risk is essential. Prevent, detect, respond; those are three key elements to live by and should cover everything from the business impact of an attack, to technical considerations on how to prevent them and how you’d respond in the event of an attack.”
Legacy system concerns
The hack has also highlighted concerns about whether legacy systems are robust enough to cope with the sophisticated attacks now targeting the financial services industry.
Recent hacking victims have included Italy’s largest bank, UniCredit, which suffered a data breach involving 3 million records last year, and Equifax, although both suffered lost data rather than facing ransoms.
A recent report from Accenture claimed that around 80% of organisations are introducing digitally-fuelled innovation faster than they can secure it against cyber-attackers.
Michael Kent, chairman and co-founder of digital money transfer service Azimo, said: “Unfortunately these targeted and sophisticated malicious activities are becoming more common, with legacy finance businesses especially vulnerable.
“The new breed of fintechs have invested in far more robust infrastructure, systems and processes to minimise the impact of hackers. It's something else the legacy players should take on board, learn from and imitate. Security breaches of this scale are hugely damaging to the whole industry reputation, destroy value for the companies impacted and worst of all, create a nightmare for customers."
However, industry experts also point out that securing systems may not necessarily require a radical overhaul of technology and software. The key is robust processes, constant vigilance and an eagle-eye for detail.
Pascal Geenens, a security researcher at Radware, a network and application security specialist, has discovered numerous hacks that have beaten business firewalls in the past.
He argues that regular and relatively straightforward security patches could prevent attacks, adding: “In terms of prevention, it’s not ground breaking. It’s about the basics, such as staying on top of software management and having robust real-time detection and mitigation in place. Unpatched systems are an invitation to organised crime groups. Patches need to be applied as soon as they are available.”
A critical component of robust IT security is employees. They need to be trained to spot dangerous emails that include links to download hidden software or aim to persuade staff to reveal their login details and passwords.
In addition, systems also need to be in place to spot any rogue employees trying to help hackers.
Alan Stewart-Brown EMEA vice-president of Opengear, a company that provides technology to several banks, recommended that companies introduce systems that ensure network resilience in the event of a successful attack, by quarantining affected parts of the network, so other systems can be restarted to maintain service levels.
He said: “Network resilience technology such as smart out of band systems (OOB) can be used at remote sites or branches to ‘air gap’ the network from the outside world, determine which specific equipment had been affected and then keep that totally isolated.”
If a large business suffers an attack, there may not be enough employees available to resolve all the problems caused by a global outage. Using a smart system resolves this problem because essential services can remain online while resources are focused on defeating the affected areas.
The legal perspective
Data breaches can also have significant legal implications, particularly following new legislation such as GDPR, which is designed to ensure adequate protection of customer data and punish companies for security failures of breaches.
Jimmy Desai consultant solicitor at Keystone Law said: “Companies that are handling money online such as banks and foreign currency exchanges often attract the attention of hackers as these kinds of companies may find it particularly difficult to operate without fully functioning IT systems and hence may be vulnerable to the demands of hackers.
“The main lesson to be learnt is that companies should have data breach plans in place so that if a data breach does occur then there are alternative systems or ways to continue operation.”
Brian Craig, legal director at UK law firm TLT, urged companies to take action before it is too late.
He said: “In response to the growing threat from hackers, organisations of all sizes have been equipping themselves with the resources and expertise necessary to address privacy and cyber risks. However, we have seen many businesses taking an uncoordinated approach to the implementation of cybersecurity protocols, leaving them open to vulnerability from this fragmented approach.
“Implementing a governance strategy with an accountable cybersecurity leader in place would likely provide greater resilience against attacks and data loss, and allow for a more coherent, business-wide response should an incident occur.”
Graham Thompson, chief information security officer at law firm Irwin Mitchell, added: “For any business that is online today the message is loud and clear - have a cyber security strategy and invest in it. Cyber is not an IT problem, it’s a business-busting risk.
“No matter how good you think your defences are, no matter how much you spend on cyber security, remember to prepare for the worst.”
Six step-plan to combat cyber-attacks
Internet security company Kaspersky has published a six-step plan to prevent successful cyber-attacks on companies.
The plan focuses on key principles such as good processes, effective monitoring and ongoing staff training.
David Emm, principle security researcher at Kaspersky, said: “The ongoing impact of this security breach serves as a stark reminder for businesses to adopt and maintain robust cybersecurity policies and procedures.
“Even if a company on the receiving end of a ransomware attack declines to pay a ransom, cleaning up its systems, restoring data and ensuring business continuity is an involved and costly process.
“This development also poses the question: should companies ever pay a ransom to cybercriminals? Whilst the decision to pay to restore valuable data is entirely a decision for the victim, it is important to remember the following: you can never entirely trust cybercriminals to keep their end of the deal, and in paying large sums to them, you are helping to fund cybercrime and making ransomware a more lucrative business in the future.”
Avoiding ransomware attacks – a six-step plan
- Secure the business using robust security solutions, and keep all software up to date.
- Make sure to apply security updates to your operating system and applications as soon as they are available.
- Regularly run a system scan to check for possible infection.
- Back up valuable information.
- Ensure that access to corporate systems is secure and that robust authentication mechanisms are in place, including the use of two-factor authentication.
- Educate your employees about the risks associated with opening up dangerous email attachments from unknown sources, as well as the importance of maintaining strong passwords.
Cyber kidnap – what is the right response?
Karen Holden, the CEO of A City Law Firm, provides expert advice on what to do if the worst happens.
The modern-day kidnap is cyber data being stolen.
Should companies like Travelex really proceed to pay a ransom sum to prevent personal data from being released?
The advice is NO - they should not, as this type of money continues to assist these type of data hackers and enables them to be funded to target other companies.
What can companies do to prevent this happening and how to companies cope?
Some companies refuse to deal with them and make the attack public immediately by a lot of companies decide to pay the hackers.
It is a growing industry – these are serious businesses that conduct this attack and they make millions of pounds by hacking into companies. This is a serious risk for UK businesses. It puts businesses out of action and is a massive problem in the digital world.
We are very reliant on digital communications these days.
This is the first attack of 2020 so far, but we are sure that it will not be last attack we hear of and how the Information Commissions office will get involved in this matter is yet to be seen.
The main advice is to NOT pay up as it will encourage more crimes to commence.
- Ensure that you keep policies and systems up to date and compliant with the GDPR and DPA 2019 legislation.
- Keep software up to date
- Have anti-virus software in place.
- Install systems that monitor your systems and that can react immediately.
- Keep backups of data.

